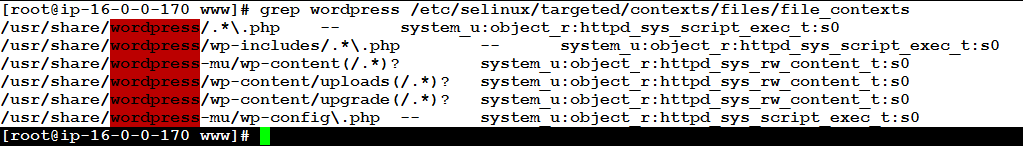
SELinux can be such a nuisance. In particular, if you have a newly created file system, you will need to add labels to it, also known as SELinux security contexts.
Cyber security, infotech
Filipe Martins Leave a Comment
SELinux can be such a nuisance. In particular, if you have a newly created file system, you will need to add labels to it, also known as SELinux security contexts.

In the age of cyber warfare, being paranoid is the only reasonable attitude and that means, among other things, being paranoid about software updates.
If you are running Linux kernel 3.6 or newer, anyone in the world on a network that allows IP spoofing can hijack your encrypted communications in less than a minute, with a success rate of 90%.
Here is how to fix it.

Over the years, Apple has dismissed some of their best technical talent. Today, it came back to bite them: the legendary electronic maker had to admit that they got hacked big-time, joining Seagate in this predicament. It made news all over the airwaves.
Filipe Martins Leave a Comment
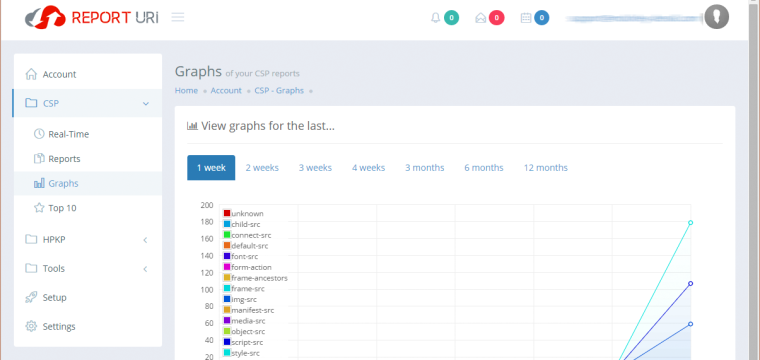
[Updated 2019-03-17] Are you wondering why some JavaScript code from external domains simply won’t execute on your website? The reason could be as simple as an overly restrictive Content Security Policy (CSP for short). This article explains how you can create a Content Security Policy that’s both protective and functional. It will help you to secure your web server from some types of cross-site request forgery (XSRF/CSRF/XFS), clickjacking and other code injection attacks.
©2022 CybrAnalytiqa OÜ