There are two major no-nos when it comes to writing NGINX redirects:
- thou shalt not use
if statements(that’s a major no-no); - thought shalt not use
rewrites(they are a waste of resources, as in “slow” and “expensive”).
Instead, use ol’ good location blocks. But what if you have plenty of URIs to redirect? How do you deploy RegEx magic with NGINX? Easy.
For example, in order to eliminate the year, month and day from an URL, use this (updated!) regular expression:
location ~ /magazine/(\d\d\d\d)/((\d\d)\/)+(.*){
return 301 http://$server_name/magazine/$4;
try_files $uri $uri/ /index.php?$args;
}
The first capture group (\d\d\d\d) represents a four-digit year, the second and third are nested and capture the month and the day (if available), followed by a forward slash and zero or more occurrences of any characters (.*). The return directive will output only the fourth capture group [$4] that is defined as any number of characters other than the line break (.+). The important thing to note is the fact that NGINX does not insist that you mask forward slashes (/) for reasons of simplicity (except when used in a capture group between brackets), yet it still counts capture groups the way you would expect it to.
In case of doubt, you may want to refer to an online regex editor such as regexr.com or regex101.com. For those who need to refresh their regex memory, here is a nice cheat sheet for regular expressions.
Restart NGINX to apply configuration changes. (So far so good!)
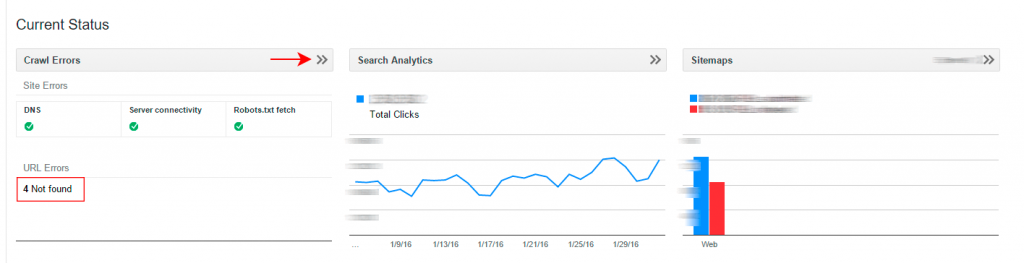
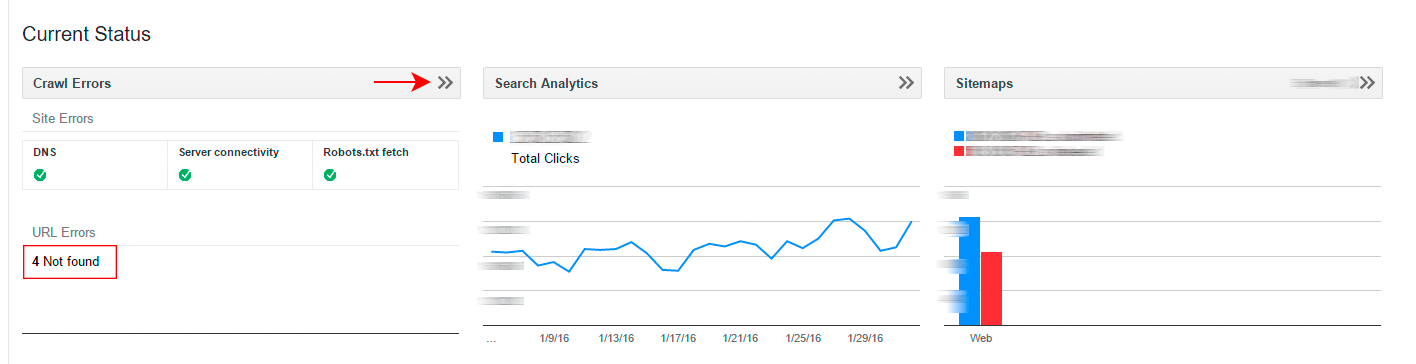
But what do you do to ensure that you haven’t overlooked some God-forsaken URLs that will deliver nasty 404 errors until the cows come home? Easy: check the errors in Google Webmaster Tools (and also, read your email: should you mess up in a major way, that’s where Google will complain, just before penalizing your site). Even if crawling failed only intermittently, it is still advisable to mark Google’s complaints as resolved once they have been resolved, obviously.
To verify if your 301 redirects are working, check out this post: SEO Secrets: How to Verify that Google Respects Your 301 (and 302) Redirects, Ranking-Wise.
Leave a Reply