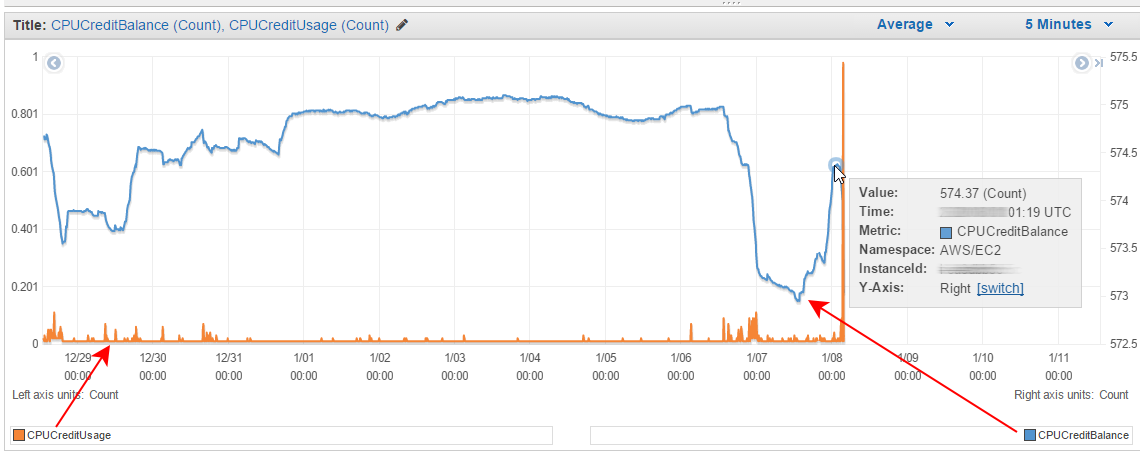
For workloads that don’t require a consistent CPU performance but do experience spikes in service demand, Amazon’s AWS EC2 service offers Burstable Performance Instances. Their competitive pricing can contribute to considerable savings and improve service availability, but how do you know if you are getting a good deal? You don’t, unless you are able to verify your CPU credits usage and the remaining balance. Here is how to figure out what’s really going on.