The versatile advantages of NVMe are becoming increasingly apparent in modern storage systems. You can take advantage of them in the cloud.

Cyber security, infotech

The versatile advantages of NVMe are becoming increasingly apparent in modern storage systems. You can take advantage of them in the cloud.

Intel (INTC) is getting close to a deal to buy the Israeli-based chip foundry Tower Semiconductor (TSEM). The foundry saw its shares go through the roof late Monday by as much as 50%.

For quite some time it seemed as if cyber vulnerabilities in the Java ecosystem would be losing ground. Instead, it was the calm before the storm: a vulnerability in the Log4j library threatens web servers and other applications in a variety of ways.

Finding errors in a postfix log file is tedious work. The job gets even more complicated if you have to dig through old postfix log files which might no longer be relevant. logrotate comes to the rescue, but only if you configure it correctly. Here is how you can do it on Fedora.
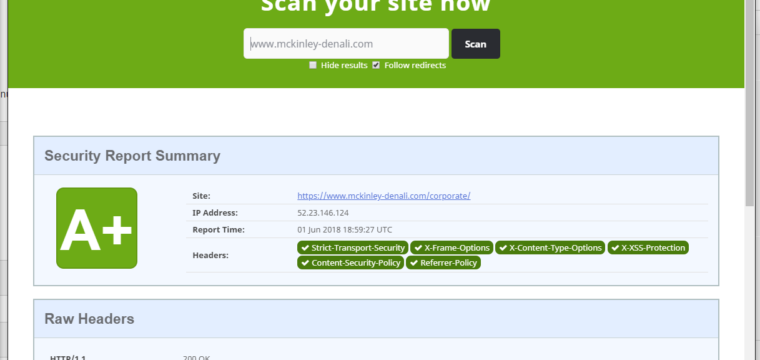
[Updated 2022-11-30] This post explains how to set up robust security headers in NGINX to protect your web application from malicious payloads and other forms of attacks. Choose your HTTP(S) headers wisely.
©2022 CybrAnalytiqa OÜ